The book is available as an open publication on this link and available for purchase online the paper copies of the first edition are sold out. Laczkó Juli: The Art of Hacking, Intersections between Hacker Culture and Visual Arts Publisher: […]
March-April 2026: participation in the clay pcb making workshop by Stefanie Wusitz and Patricia Reis April: group exhibition RE(NEW) (solar crawlers) at esc medienkunstlabor, Graz May: group exhibition (Where we’re at) and lecture (ACAB) at AMRO, Linz
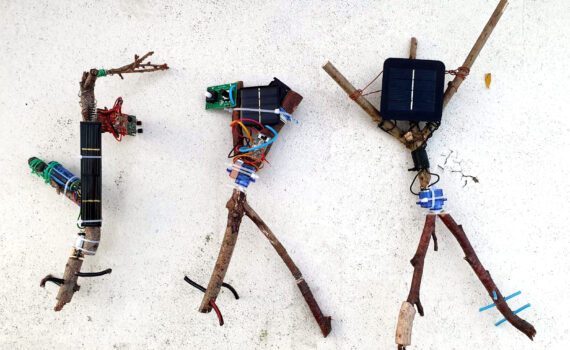
made for esc medien kunst labor, for the exhibition Out of Control II, 2025 autumn, in Graz, Austria The solar crawlers are simple, little off-grid robots made of scavenged electronics and wood. They are activated or charged by sunlight and […]
All Computers Are Broken: rethinking the Technosphere Along the Lines of Repair and Maintenance Work
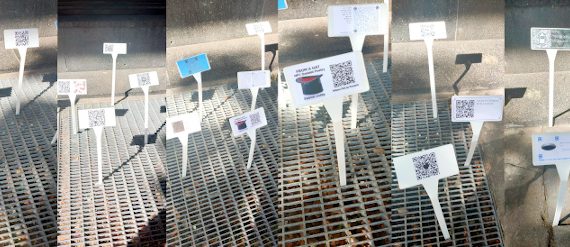
#nfcdab is a DIY or DIWO [DO IT WITH OTHER]? A digital art biennial that uses wireless technologies, light waves and electromagnetic fields, such as Wi-Fi routers, QR codes or NFC tags to access content. The idea behind the biennial […]
Featured by Amsterdam Alternative, OT301’s agenda and Instagram; 6-8 December 2023, 4bid Gallery, Amsterdam, Overtoom 301. I was very proud to present my work ‘Where we’re at’ (‘Ott, ahol mi vagyunk’) in Amsterdam’s 4bid Gallery in December 2023, as a […]
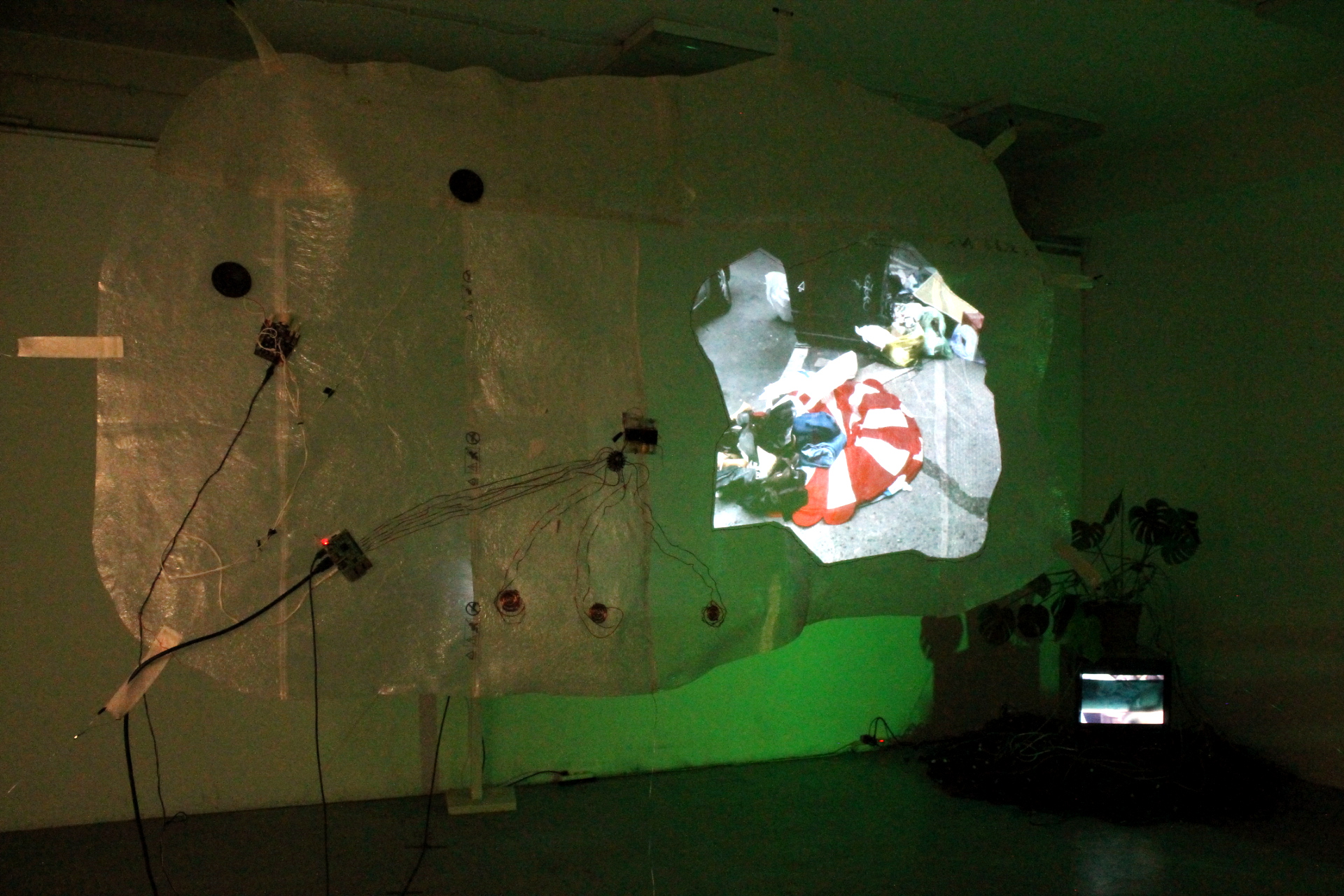
Interaktív installáció, Igor Metropol Stúdió, Budapest, 2022 december – 2023 januárMunkabemutató / open studio: január 18. (scroll down for English) A munkabemutatón Szabó Eszter Ágnes képzőművésszel beszélgettünk a lomizás/bolhapiacok képző-, és médiamüvészeti vonatkozásairól. Magyarország a szemét ökonómiájának tekintetében (is) két […]
The THF, or Trans Hack Feminist Convergence brings together FLINTA contributors of technofeminist infrastructure practices. In 2022, it was hosted by Calafou. I conducted a discussion based on two inspiring text I recently studied:
NFC is short for Near Field Communication. BrowserBased and Noamata co-organized several Near Field Communication Digital Art Biennale-s in Europe over the last decade. In 2022, a series of new NFCDA instances are appearing all over Europe. I participate with […]
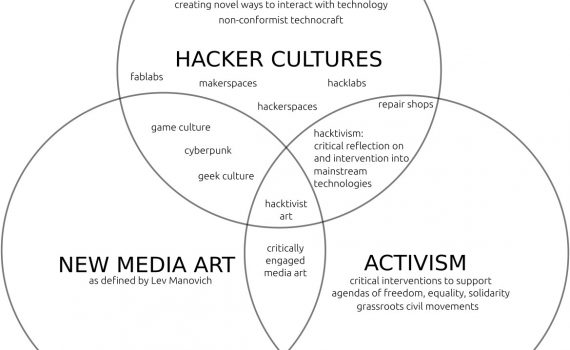
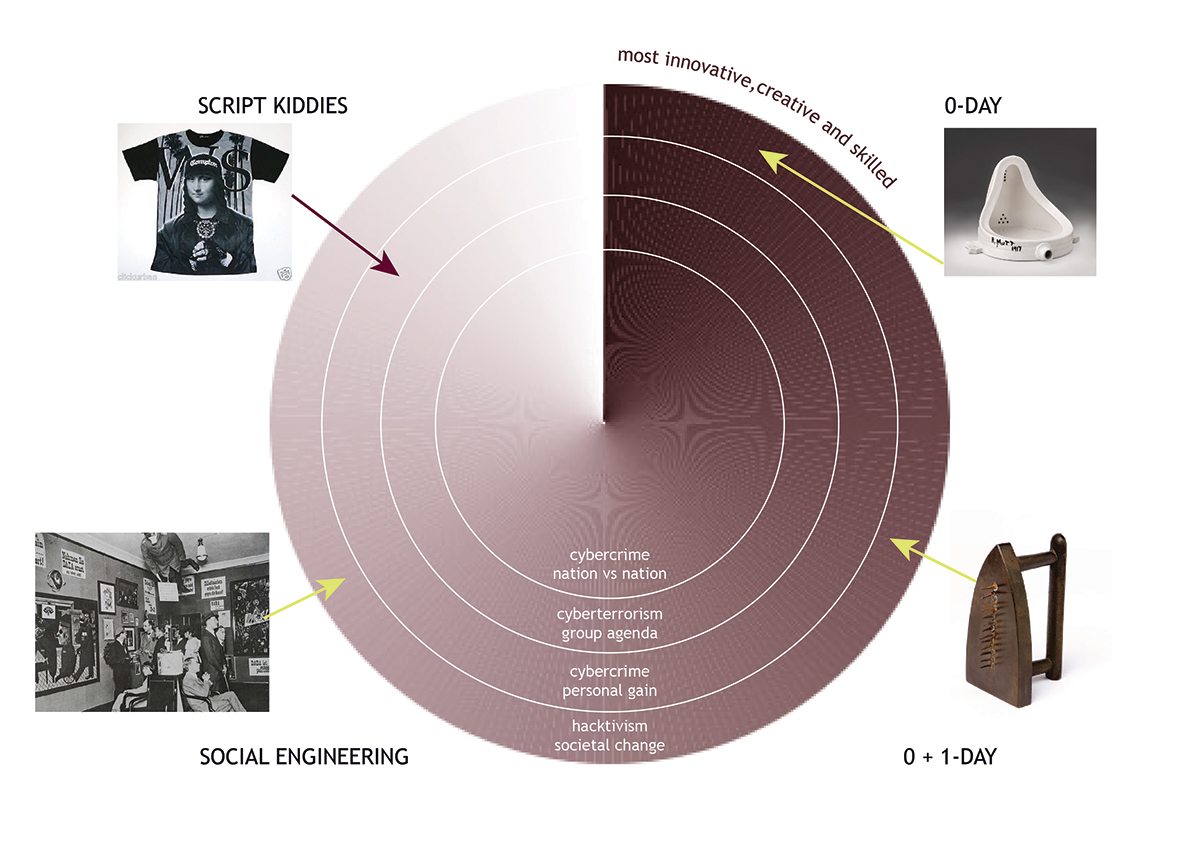
Recently published by the Institute of Network Cultures Amsterdam, on the relationship between the historical avantgarde and hacker cultures
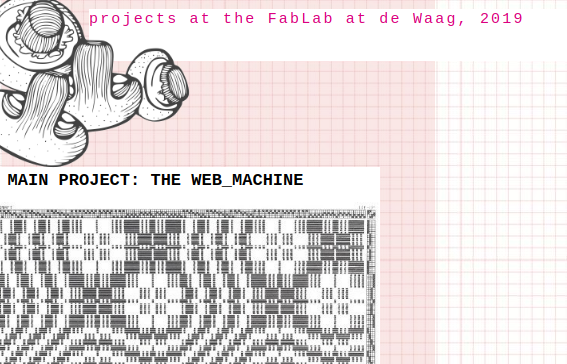
Proud to be one of the contributors to Siggraph: Digital Power, Activism, Advocacy and the Influence of Women Online exhibition. If you play my browser-based loom woven in python, you can save your encrypted text to your desktop as a […]
Made @Calafou, Catalonia & Amsterdam, Technologia Incognita and LAG, 2019 December, Amsterdam bio-hacking workshop @ Hogeschool voor de Kunsten Utrecht, Creative Tech Club with PinGui, BiohackDag @HKU IBB, Feb 2020 joining the Anarchist Village at 36c3 2019 PinGui’s lights synchronized […]
exhibition @ Joe’s Garage, Amsterdam, opening: 28 November 2019 The work is a manifestation of the tension between the imaginary forms and functions of the vast space of Calafou, once an industrial colony and thread mill, now a post-capitalist, eco-industrial […]
September-October 2019 Learning to use the laser cutter: trace bitmap, outlines only, a combination of cutting and engraving on 3mm plexi.Llearning to use the vinyl cutter. option of printing from linux and windows os available on same dedicated pc. linux […]
Plastenka was an ecodesign label that I founded and run in Budapest between 2010 and 2020. It produced a total of 842 bags and accessories, including, but not limited to courier bags, wallets, laptopskins and backpacks, made of upcycled plastic […]
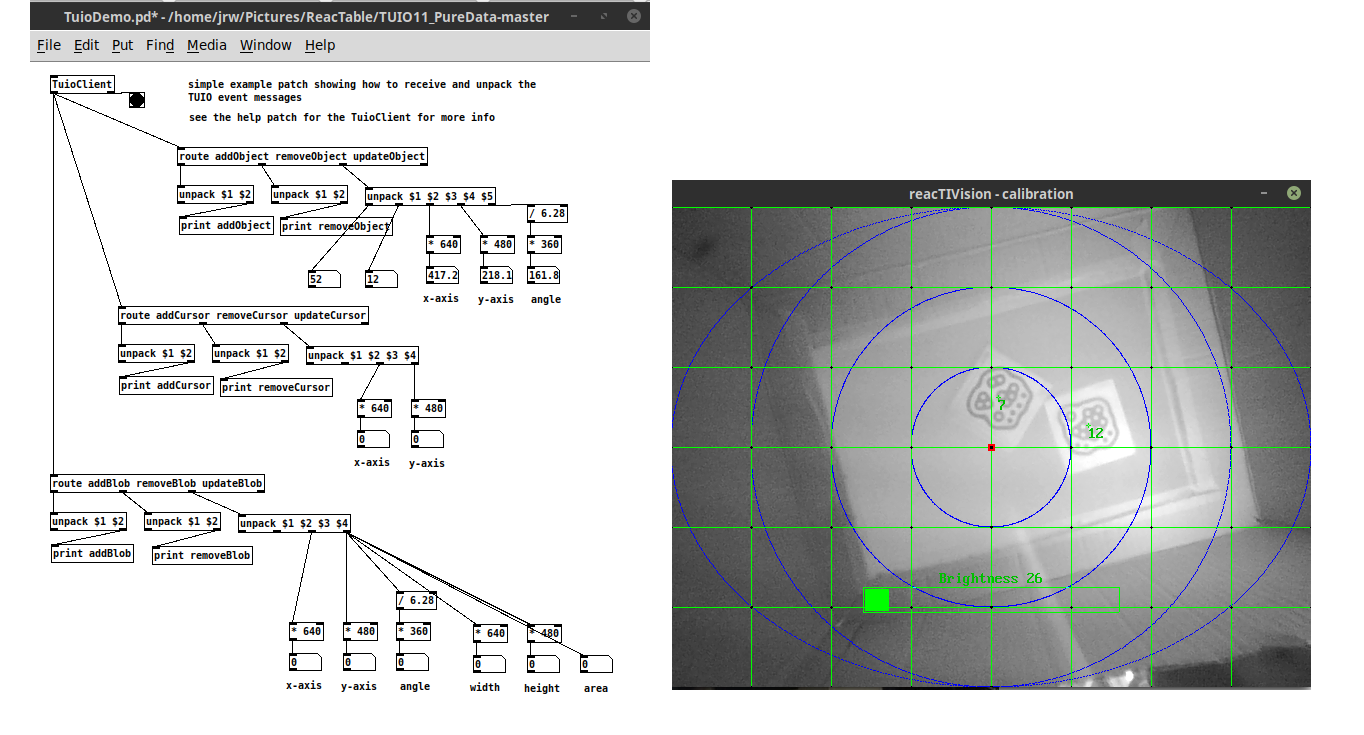
implemented at Budapest Metropolitan University, 2017-2019: Introduction to Hacker Cultures and Culture Jamming (seminar/practical) (HU and ENG)Hackerkult-compressed Interaction Design Course: Building a Reactable (seminar/practical) (ENG)Reactable Course Introduction to Media Design Theory (lecture) (ENG)MDT curriculum pictures of the reactable building course:
Eight of the portable upcycled shelters have been made and given away to homeless people with the financial support of MKKP, the Hungarian Two-Tailed Dog Party. The anonymous distribution was facilitated by social organizations, and the production was done by […]
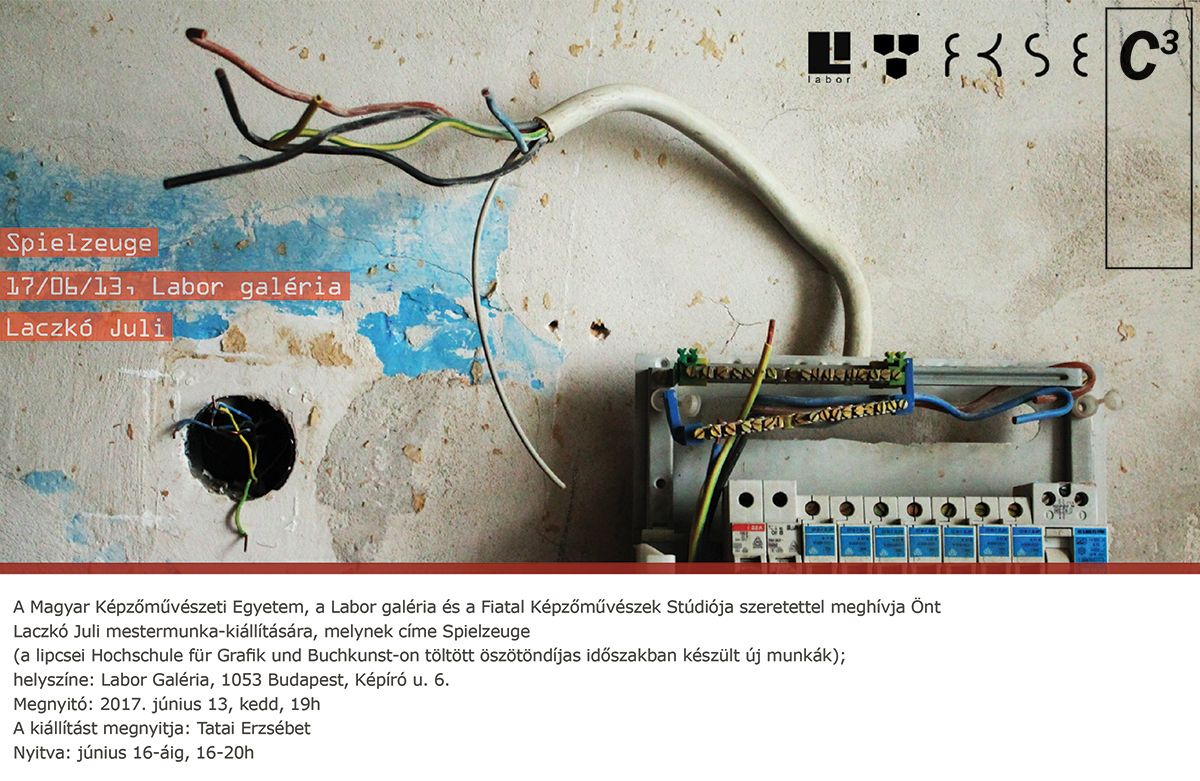
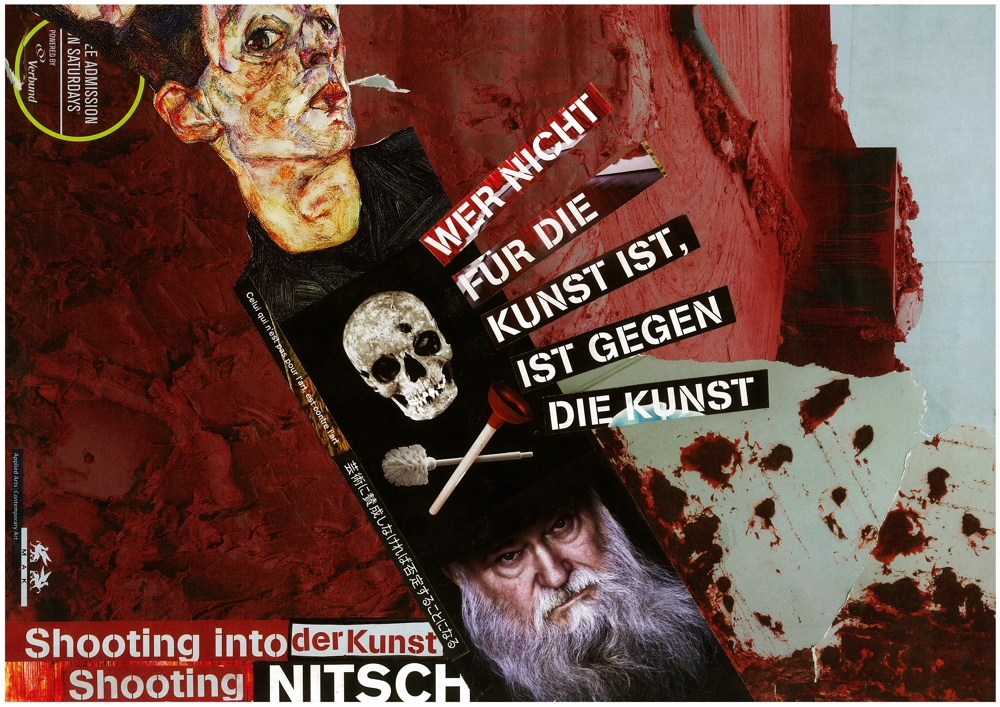
recent publications of works in exhibition catalogs include DLADLA, MKE DLA exhibition on the centenaire of Cabaret Voltaire, 2016, Budapest I spy with my little eye, Gapgap, Leipzig, 2016 Error: MKE DLA exhibition, 2014, Dunaszerdahely, Slovakia
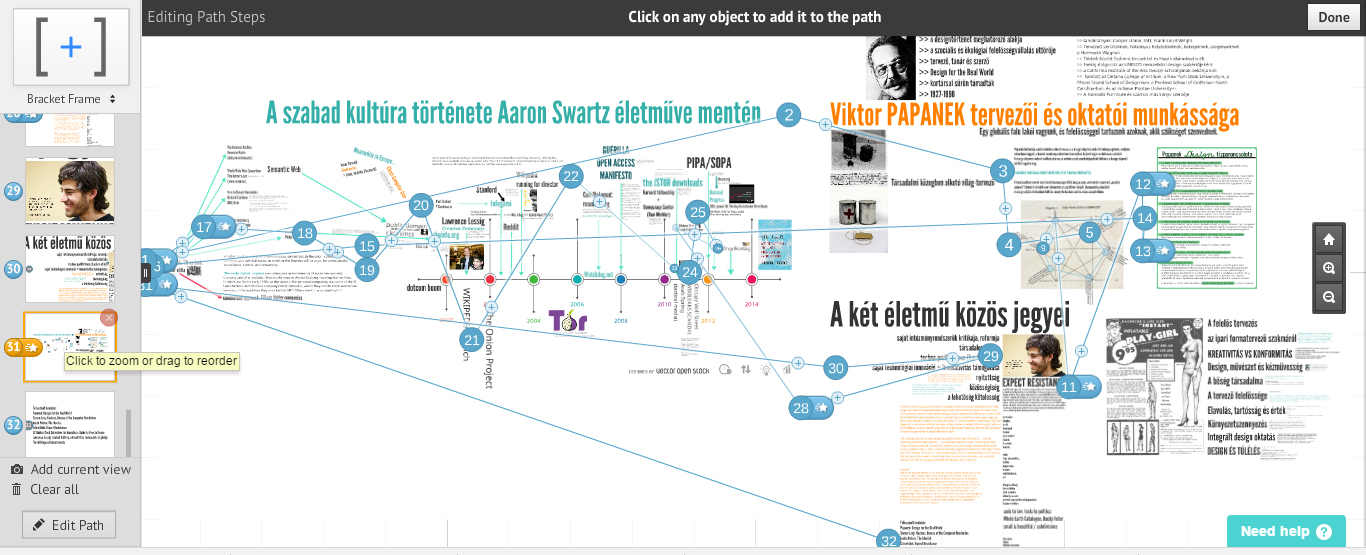
As part of my obtaining my absolutorium, I presented and compared the oeuvres of Aaron Swartz and Viktor Papanek at the Hungarian University of Fine Art’s Doctoral School in 2017. The presentation in Hungarian The Legacy of Aaron Swartz in […]
MKE DLADLA This work was created for the exhibition of the Doctoral School of the Hungarian University of Fine Arts, on the occasion of the centenary of the Cabaret Voltaire, founded in Zürich in 1916. ‘in 2020, Trump’s US and […]
HGB Rundgang 2016, Alles in Ordnung(part of the exhibition of Class of Photography in the Field of Contemporary Art, prof: Peter Piller)11-14 February, Hochschule für Graphik und Buchkunst Leipzig Bordering conscious collecting and hoarding disorder, my studio held a huge […]
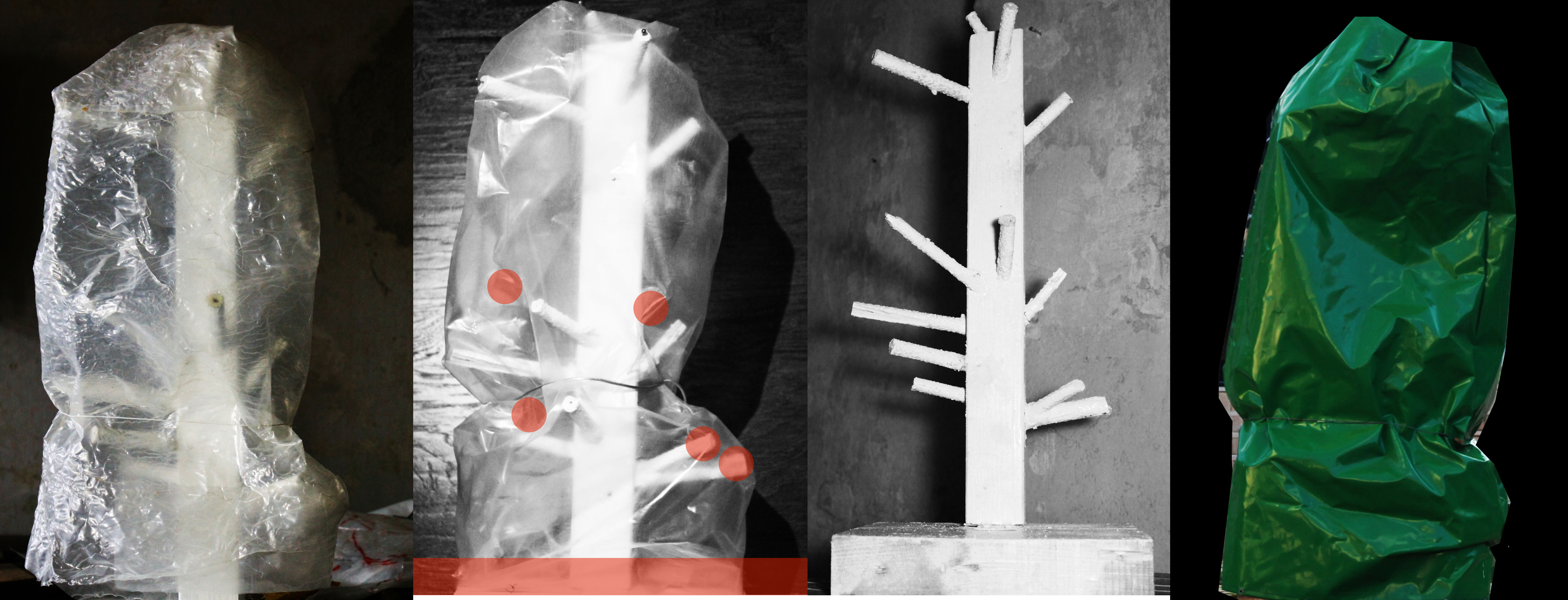
I spy with my little eye #25-12 February, Gapgap, Leipzig, group exhibitionUndercover, object mapping and photo documentation, 2017 Budapest; wood, upcycled plastic, students’ drawings, projection In Budapest, through the winter, many public sculptures are covered by plastic overlay for weather […]
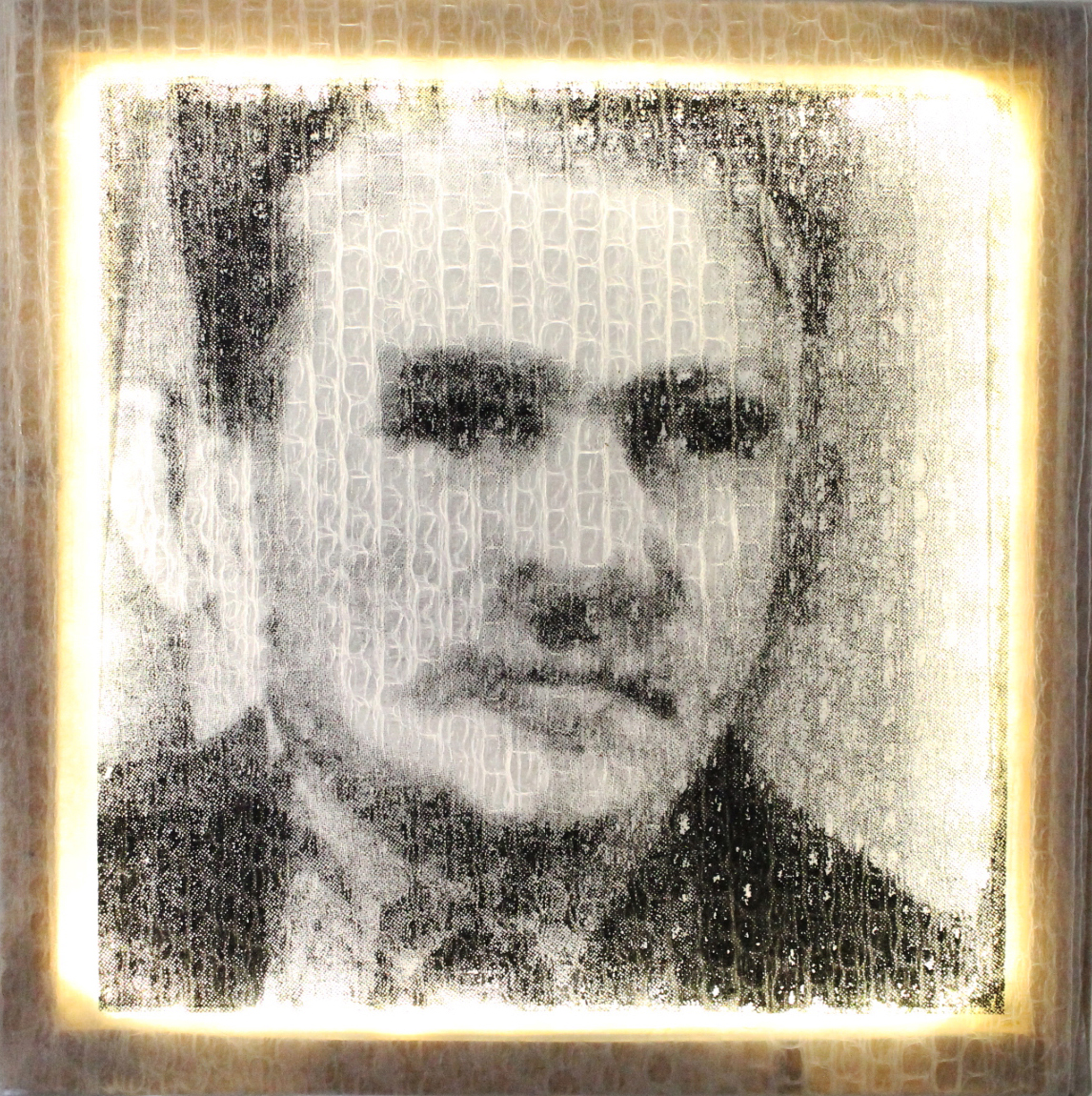
UTOPLAST lighboxes, 2016 Leipzig, 2017 Budapest; sewing, silkscreen, projection, utoplast, wooden framesMorphing portraits of nine infamous, now-dead dictators, I wondered what are the common features of portraying them. I useddifferent media to create different types of morphs: one sum of […]
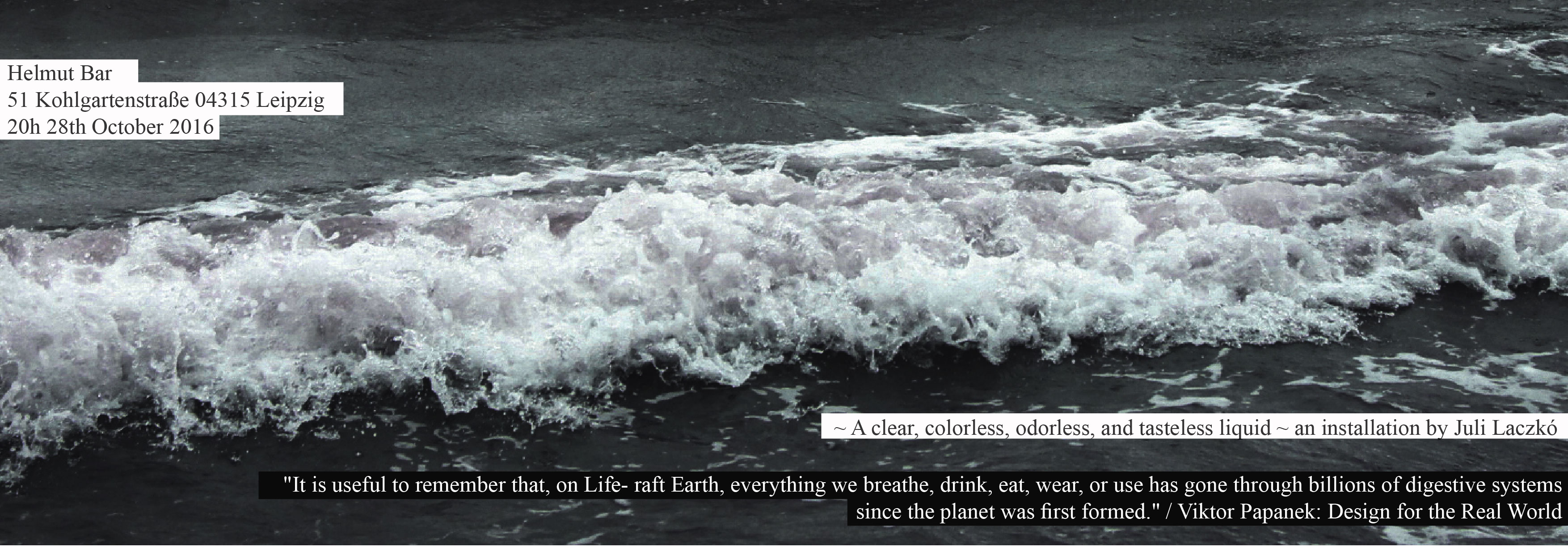
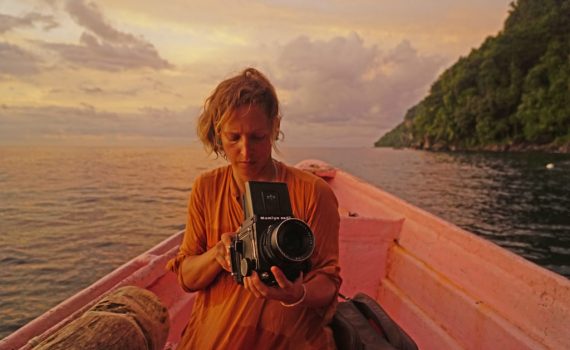
28 October – 9 November 2016, Helmut Bar, Leipzig, curated by Maeshelle West-Davies I dedicated my first solo exhibition to wondering about and on water. I have crossed the European border from Greece to Turkey in 2016 at Lesvos by ferry. […]
A group exhibition – a group exhibiting (itself): presentation of a “we” that mistrusts itself; the random encounter (collision?) of travelers in the same city-, the same action space – reason enough for a joint project? reason enough for a […]
when living in Leipzig, I was too often asked how the step-by-step deterioration of democratic cultural institutions has been done in Hungary since 2010. I responded with this handmade infographic that details the process from the bottom up from 2010 […]
My arrival to Leipzig in the fall of 2015 coincided with the arrival of a wave of refugee people. In my wondering about ‘wir schaffen das’, I re-created a selection of Richard Scarry’s Busy busy town’t language teaching illustrations, this […]
In 2012, I participated in the Remix Culture Summer School in Amsterdam, at the Amsterdamse Hogeschool voor de Kunsten, organised by Emiel Heijnen. Throughout a series of workshops, I designed the short course ‘Hack Your Hood’, which I implemented in […]
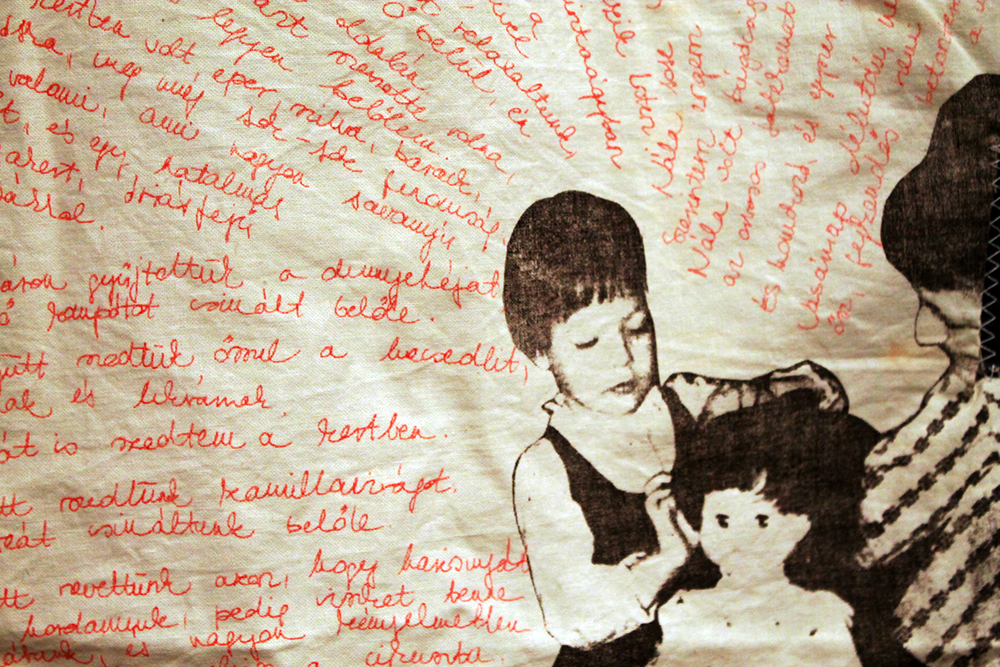
Family History research, different installations,canvas, projection, silk-screen, sewing, Marseille and Budapest, 2006-2008 (canvas dimensions: 2x2m)
Juli Laczkó DLA Born in Budapest, Hungary, 1985E-mail: laczkojuli@gmail.comLinkedInIG Current position:Teacher IMT and coordinator of Media seminars at HKU Media, Image and Media Technology (Hogeschool voor de Kunsten Utrecht) Previous positions:Teacher at Situated Design, Master Institute of Visual Culture (Avans Hogeschool, […]
UTOPLAST Jurt, diameter: 5 m, 2012. Bamboo structure: Kjartan CodeThe Jurt was donated to Migration Aid in August 2015, when large numbers of refugee people were hosted at Keleti Train Station, Budapest, to serve as a mother-child space.
UTOPLAST water diversion and shade system, part of Eco Tango Garden for Bloom garden show in Ireland, designers: Tünde Szentesi and Svaja Vaicula, 2013 UTOPLAST vízelvezető és árnyékoló installáció a Bloom írországi kertészeti kiállítás részeként, ezüst érem, kategoria gyoztes, kiskert […]
Prototype of packaging and storing system for donating excess food. You can pick up the flat sheets from the supermarket, different colors for different types of food, to fold them and pack leftover food into and dispose of the boxes […]
terMINI 2013: foldable mobile homeless shelter made of UTOPLAST, solar lighting, plans and prototypes exhibitions: Hiba és társai, DunaszerdahelyFinom különbségek, Pozsony, 2014Termini Public Pilot Eve, 2014terMINI facebookA termini hatásmechanizmusa a nyilvánosság terében Main press articles in Hungarian (most others are extracts […]
Interactive upcycled art installation for Burning Man 2011, UTOPLAST cover, 2011, Black Rock City, Nevada, USALead artists: Zsolt Ádám, Péter Debreczeni, Dániel Feles, Juli Laczkó, Andrea Sztojanovitson FacebookHVGTop 10 magyar design
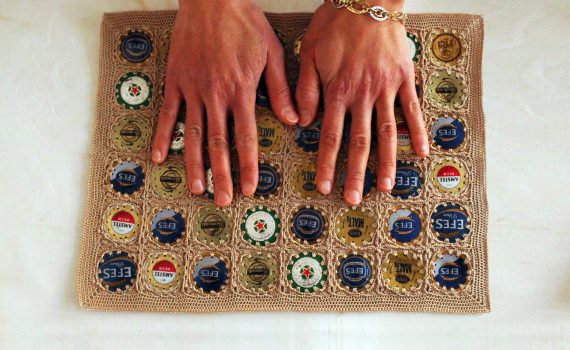
Elyne Saglik, photoshoots at Cöp(m)adam, Ayvalik, @A dolgok állása, Veszprém Várgaléria, 2014.Cöp(m)adam is a social enterprise in rural Turkey where women craft goods by upcycling different materials. I wanter to photograph what they are proud of, and they decided to […]
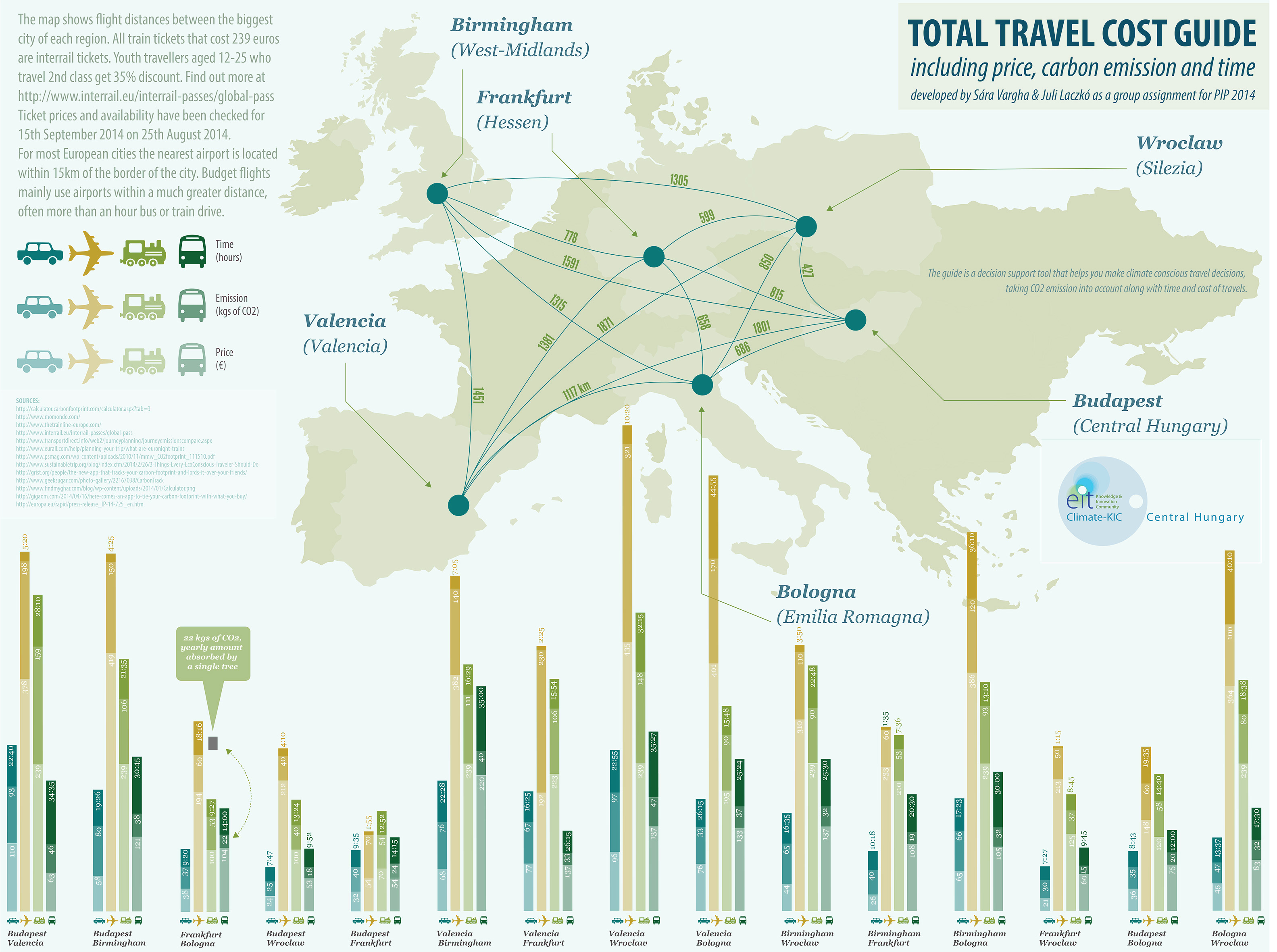
As a Pioneers into Practice grantee, I assisted a Kitchen Budapest Talent Program team with videography and mediadesign work in 2014. Process documentation
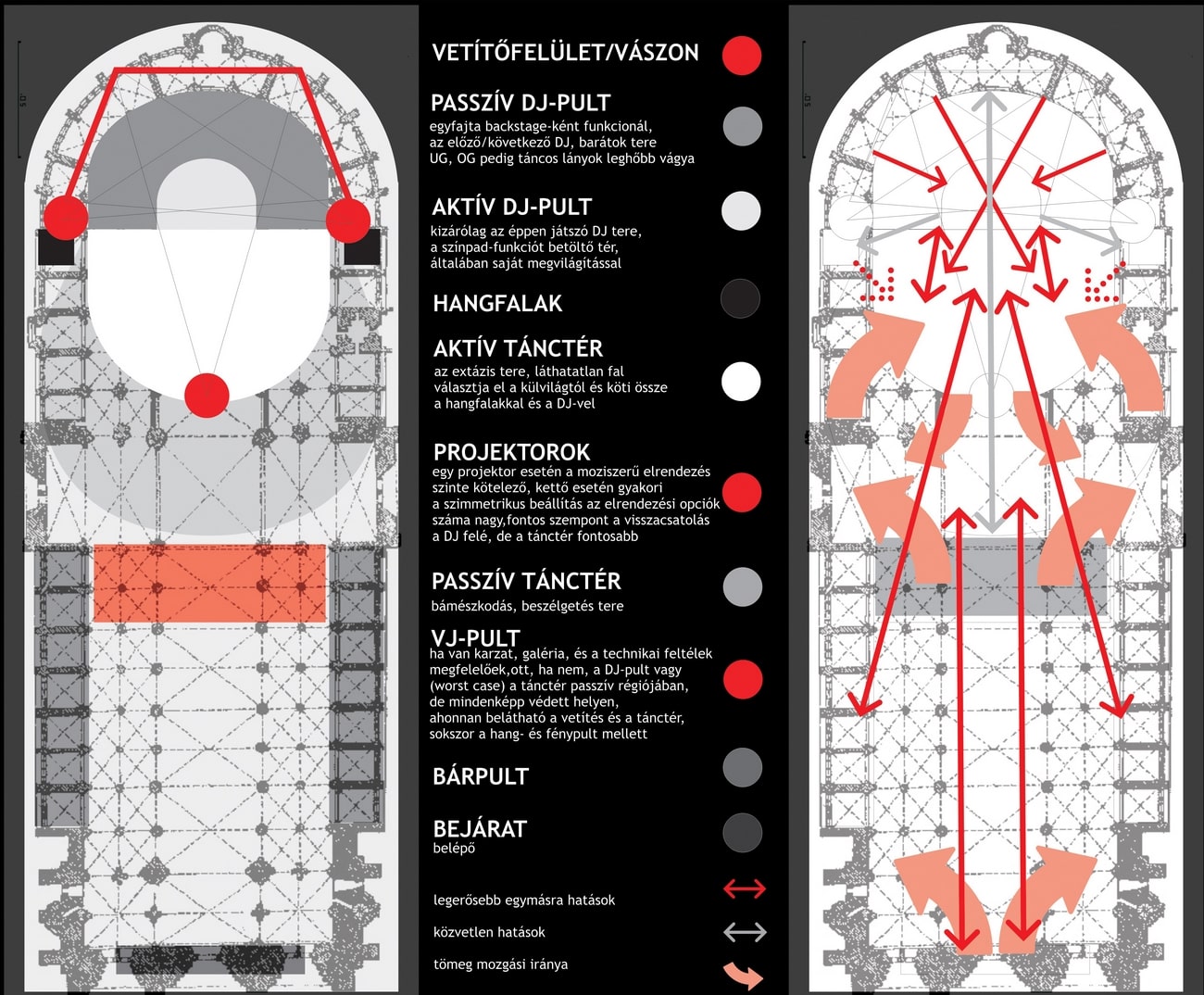
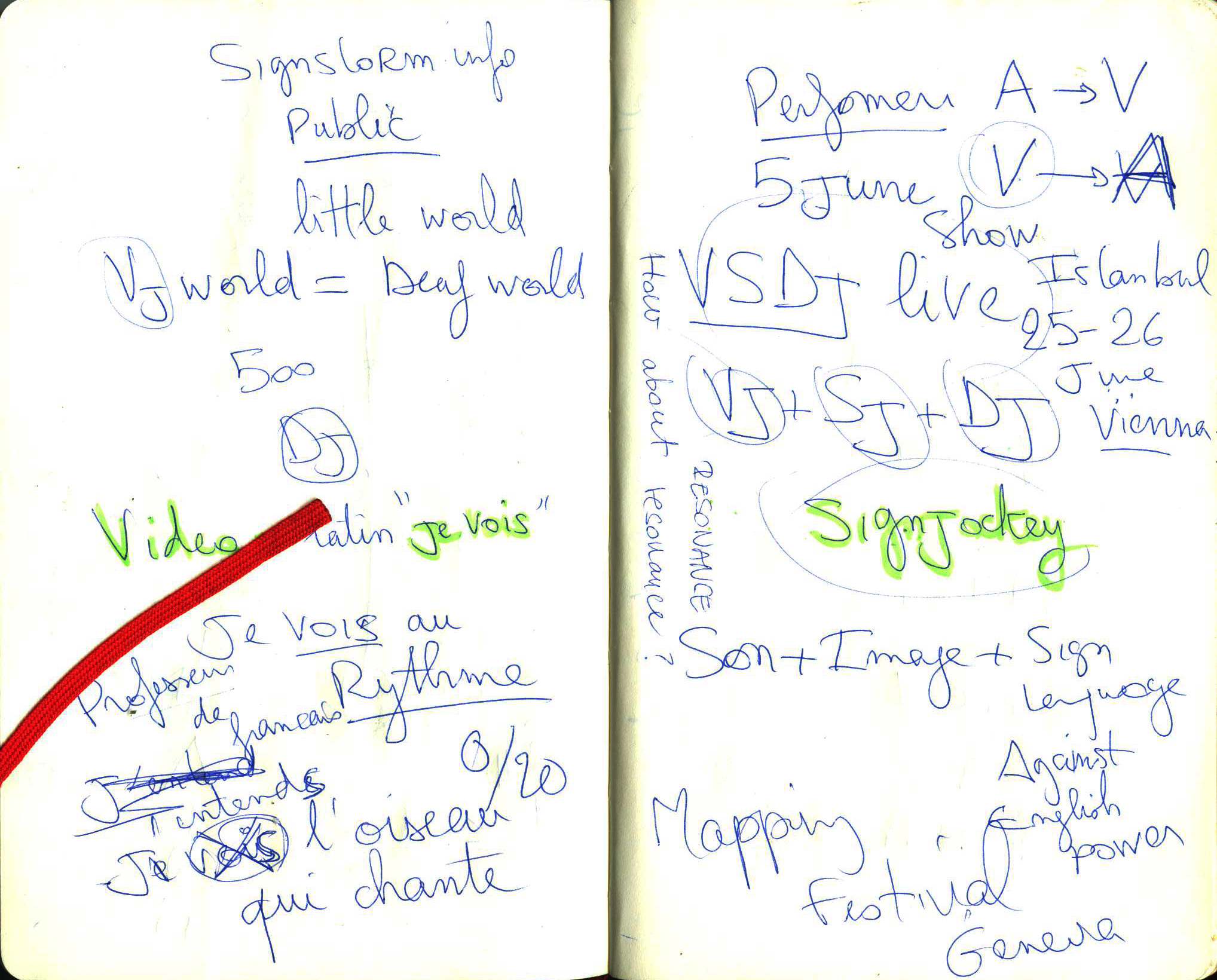
Loopé was a collective of Dani Halasi and Juli Laczko, at times joined by Esteban de la Torre and Gábor Karcis, working with projection, video, performance, and different media in space. VJs since 2003, collective 2006-2013, created several party and […]
„Hallgasd a képeket, nézd a hangokat!” – Vizuális zene a kortárs művészetben” szimpózium Nam June Paik emlékére, Koeai Intézet, Budapest, 2012
detail from KözTest with Réka Harsányi, virtual reality research visualisation on traffic behaviour, @A dolgok állása, Veszprém várgaléria, 2014
Between 2007 and 2012, I contributed to the organization of the Hanna Hanna Festival & Art Gathering near Gúta, Slovakia. I curated, booked, and organized visualists for 5 different stages, managing riders, gear, and building rigs.
As one of the many funding members of http://muszi.org/, I created Müszi’s first introduction video, just after we took over the space:
My main goals in teaching are to involve fresh and topical themes in secondary education, to prepare students for responsible and resolute adult life through the process of creation. During my teaching practice, I intended to make my students familiar […]
As a member of the former VJ Centrum, a cooperation of several visualist collectives, I was part of a series of educational workshops on VJing commissioned by the foundation ‘Kék Pont’, whose programs fostered social change through education in vulnerable […]
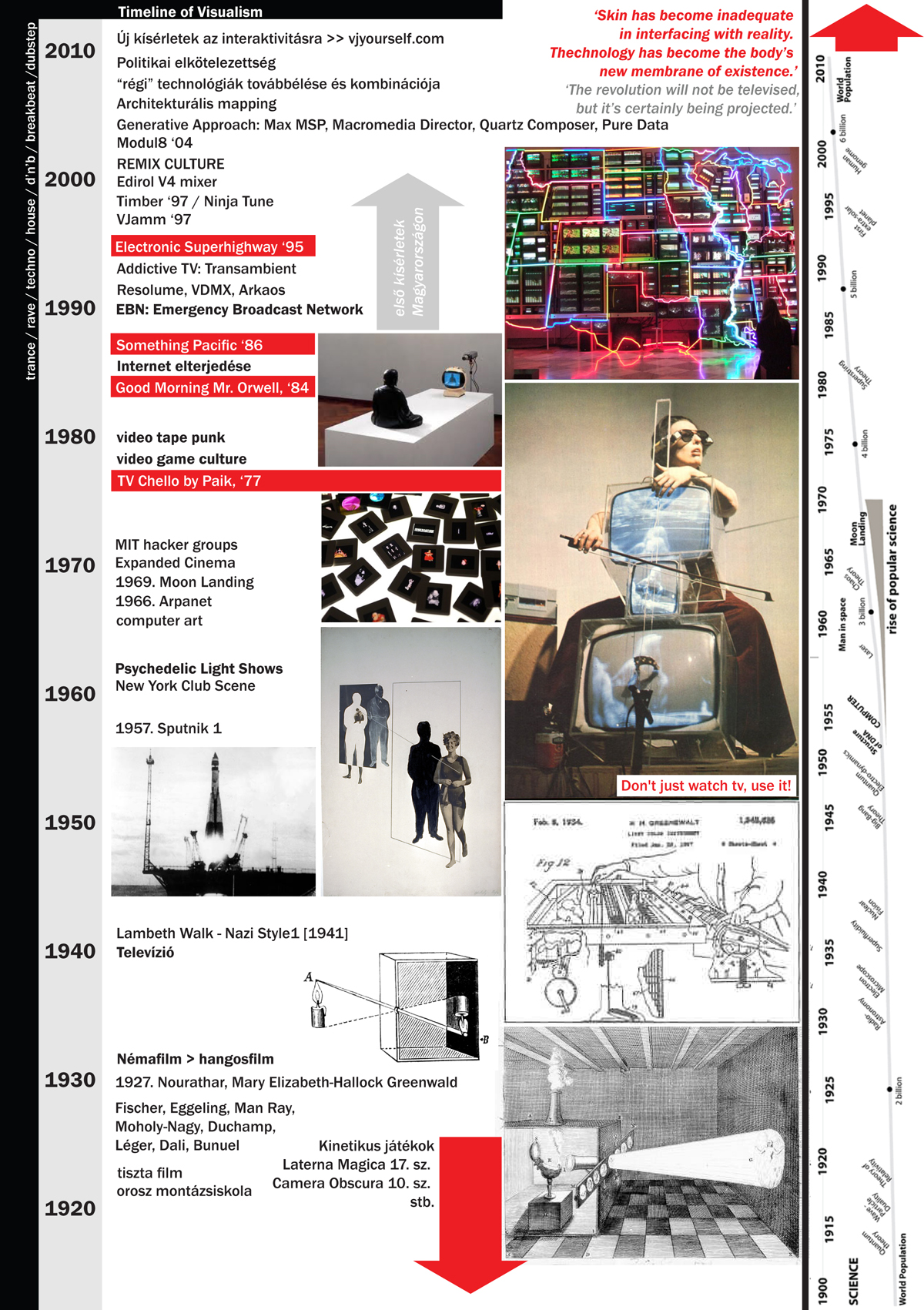
My first thesis was titled Contemporary Imaginary Rituals: Notes on VJ Culture, in which my aim was to research and discover the roots and traditions defining the visual rituals of the visual culture related to contemporary electronic musical events. The […]
interactive blind audiospace based on the novel The Helmet of Horror by Viktor Pelevin, 2010, cooperation with Zsolt Korai
Running the ecodesign label Plastenka between 2010-2020, I have designed and conducted several campaigns, both solo and in cooperation with others.
Ex Libris, visual poem and digital performance, presented in the same titled live exhibitiond: Júlia Bársony, Merlin Theatre, Budapest, 2009. Mentor: Jozef Tillmann
Family history research and visualisation, 2009, Zagreb, photos and video installation.As a CEEPUS guest student in Zagreb, I travelled to Osijek to investigate two postcards that I inherited from my grandfather’s grandmother. They are signed as from Zora, her cousine, […]
Worked as a video editor, production assistant, and media designer for the ‘House of Third Voice’, Harmadik Hang Háza, between 2009 and 2011. Our last, summative installation-performance series, Interplaces, anticipated the establishment of Müszi in Budapest. Interplaces featured over 20 […]
‘Speciális Heurisztikák’ was a group of performers I have worked with as a visualist, using static analog and live digital projection to create hybrid performances, from 2005 to 2010.
re68, 6-channel video installation, cooperation with Anita Gáspár, Balázs Sármai images used from (left to right): Fényes szelek, The Strawberry Statement, Zabriskie Point, The Unbearable Lightness of Being, The Misteries of the Organism, The Dreamers